 The Industrial Internet of Things (IIoT) promises to transform manufacturing, transportation, power generation, and a host of other industries with greater automation, new services, and more efficient allocation of resources. These advancements depend on data generated by a host of new IIoT devices now being built and deployed. But the potential cannot be realized if the data produced by the devices cannot be trusted, and that requires much stronger security than what is currently being deployed. The data is only as good as the device that generates it.
The Industrial Internet of Things (IIoT) promises to transform manufacturing, transportation, power generation, and a host of other industries with greater automation, new services, and more efficient allocation of resources. These advancements depend on data generated by a host of new IIoT devices now being built and deployed. But the potential cannot be realized if the data produced by the devices cannot be trusted, and that requires much stronger security than what is currently being deployed. The data is only as good as the device that generates it.
Cyber-attacks against industrial control systems, water treatment plants, critical infrastructure, and other IIoT networks are on the rise as is the number of devices that hackers can target. As the number of devices grows, so does the number of opportunities to hack those devices, and subsequently alter the data. The bottom line is we now have a growing number of both targets and attacks, so we must put the cyber-security solution in place to protect these devices.
Just as cyber-attacks take many forms and exploit a wide range of vulnerabilities in the target device, so too is cybersecurity multi-faceted. A fundamental, but often ignored, aspect of cybersecurity for IIoT devices is strong authentication.
The role of authentication
Authentication, for machine-to-machine communication within the IIoT, is the process of one IIoT device determining if another IIoT device is legitimate. Is the device a counterfeit or cloned device manufactured by an unauthorized third party? Is it part of a botnet sending malicious packets as part of a denial of service attack? Is it under the direct control of a hacker and being used to launch a cyber-attack? Or is it a valid device?
Authentication, then, is the process employed by an IIoT device to determine if the device it is about to communicate with is who it claims to be (is it authentic?) and if it is authorized (is the other device allowed to communicate with me, and if so what operations is it allowed to perform?).
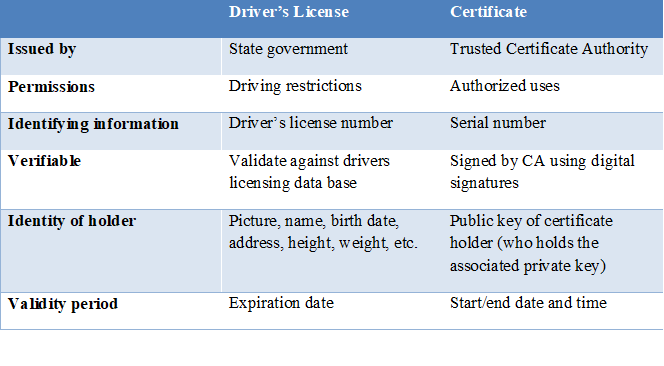
Many embedded devices use a simple username/password based method for machine-to-machine based authentication. An IIoT device will communicate with any other machine providing the proper username and password. Other systems utilize pre-shared security keys. Pre-shared keys are, in essence, nothing more than long, complex passwords.
This is problematic for many reasons. First, usernames and passwords can be stolen, sniffed, or otherwise discovered. Second, they are susceptible to brute-force attacks, in which all possible passwords are systematically attempted, and to dictionary attacks, in which commonly used passwords are attempted. Once passwords are discovered by unauthorized users or devices, they can easily be used, allowing unauthorized access and providing the ability to perform operations that should not be permitted.
In simple terms, if a device sends over the correct credentials, it will be granted access. There is no mechanism to verify that the machine should have the password or to verify if the password has been lost or stolen and password-based authentication is it is difficult to manage. If you need to change a username or password, all devices in the network must be updated, which is a significant management challenge. As the number of deployed IIoT devices grows into the millions and even billions, managing passwords becomes unfeasible.
Strong authentication for IIoT devices
To be effective, any machine-to-machine authentication system for the IIoT must overcome the weaknesses of password-based authentication. The solution must tie credentials to an identity. In other words, not only must it require the right information (password and username, authentication key, etc.), it must be able to verify this information is associated with the device using this information. And it must do so in a secure fashion. The credentials must not be easy to steal or clone, and the distribution, verification, and revocation of credentials must be automated and easy to manage.
PKI for IIoT authentication
PKI (Public Key Infrastructure) is a set of technologies and services for managing authentication of computer systems. PKI is based on a mechanism called a digital certificate. Digital certificates are sometimes also referred to as X.509 certificates or simply as certificates. Think of a certificate as a virtual ID card.
In the real world, people use ID cards such as a driver’s license, passport, or an employee ID badge to prove their identity. A certificate does the same basic thing in the electronic world, but with one big difference. Certificates are not just issued to people (users, administrators, etc.). Certificates can also be issued to computers, software packages, or just about anything else needing proof of identity.
Certificates are very useful in high security situations. For example, suppose that you needed to securely transmit data between two networked devices. How do you really know you are transmitting the data to the intended device and not to an imposter? One way of ensuring the integrity of the transaction is to use digital certificates to prove the identities of both machines.
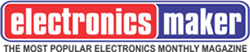
PKI provides the tools and methods required to issue certificates to all IIoT devices on a network and to manage those certificates throughout the life of a device. A certificate can be likened to a driver’s license. It provides an identity and a set of permissions, and was issued by a trusted entity. My driver’s license identifies me (Alan Grau), provides a picture to show that I am the proper bearer of the license, and defines my permissions as a driver of a motor vehicle. I am authorized to drive any standard passenger motor vehicle, but not certain commercial vehicles. And the license was issued by a trusted entity (the government of the State of Iowa).
A certificate, in many ways, is similar. A certificate is issued by a trusted entity (a certificate authority), contains permissions, and is used to identify the holder of the certificate. A driver’s license contains information allowing the holder of the license to be verified, just as a certificate contains the public key allowing it to be used only by the entity that holds the associated private key. Without getting into the details of the public/private key cryptography technology that makes this possible, an IIoT device can verify the certificate holder is the entity specified by the certificate. These services are enabled using public/private key cryptography providing the technical underpinnings of PKI. The result, which is what really matters, is a device can verify, with cryptographic certainty, the holder of the PKI certificate is really who it claims to be and not an imposter.
Certificate compared to driver’s license
Certificates, like a driver’s license, provide the basis for identifying IIoT devices. Building on this analogy, PKI provides the technology and systems to issue, renew, revoke, and manage certificates.
Limitations of existing PKI solutions
PKI is widely used within the broader Internet and as part of many IT security solutions. But PKI as a technology has drawn criticism. This is largely due to failures in implementation and security breaches with some of the Certificate Authorities involved in the management of the system. Many legacy implementations have not properly implemented certification revocation checking, resulting in expired or revoked certificates being used. Some systems have failed to properly implement certificate chain validation, which allows forged certificates to be used.
Additionally, existing PKI solutions are designed for use with public Internet and Enterprise IT networks and are not well suited to meet the needs of IIoT networks. In IT networks, certificates are issued to a small number of servers, generally via a manual process. This works because these systems implement “server authentication” using certificates and don’t implement “mutual authentication.” With mutual authentication both the client and server device need a certificate, requiring a much greater number of certificates.
With server authentication, a server is authenticated using a certificate. For example, if I log onto an e-commerce website, my web browser will validate the website is authentic using the digital certificate provided by the website server. The website, however, does not validate my browser using a certificate. It relies on a user name and password to validate who I claim to be. In some cases, a second factor authentication mechanism or other method will be used to provide a higher level of security.
PKI Solutions for IIoT
For the IIoT, mutual authentication is mandatory. When devices communicate, they must each validate the other device using certificates. Implemented correctly, no human interaction is required and using certificates eliminates password-based authentication and other weak authentication mechanisms. Digital certificates, used in this fashion, provide strong authentication. Devices are able to reliably authenticate other legitimate devices, preventing unauthorized communication with rogue devices or other unauthorized systems.
Mutual authentication, as the name implies, requires every device to have a certificate. The manual processes of legacy PKI solutions don’t scale to the needs of the IIoT and its larger number of devices.
To overcome the weaknesses of legacy PKI solutions, Icon Labs has developed a PKI solution for the IIoT. This solution allows devices to automatically and securely request new certificates, validate those certificates, and recognize when certificates have been revoked. It also implements certificate chaining support to ensure all certificates are properly validated.
Additionally, it provides management of certificates over the entire lifecycle of the device. This starts with provisioning certificates into the device during manufacturing to prevent counterfeiting and cloning of devices. When devices are purchased and installed on a network, they go through a process of provisioning. During this process, they are first automatically validated using the certificate installed during manufacturing, then issued a new certificate for use on that network. This certificate can later be revoked when the device is decommissioned.
Passwords vs. Keys vs. Certificates
Conclusion
OEMs building IIoT devices and enterprises deploying IIoT networks must be proactive by ensuring the proper security capabilities are built into both the devices and the networks in which they operate. Strong authentication of all devices within an IIoT network is one of the fundamental requirements for securing these networks.
Certificates issued and managed using PKI allow devices to perform strong mutual authentication. Ensuring the devices involved in communication are authentic and authorized is critical for securing IIoT networks. It provides the foundation for ensuring the integrity of data used for creating new business models, increasing operational efficiencies, and truly unleashing the value of the IIoT.