Mark Patrick, Mouser Electronics
IT professionals have been concerned about IT security for some time, especially as more businesses and individuals put their valuable data online. However, things came into sharp focus when the Internet of Things (IoT) came into being. To many, each of the billions of connected devices performs a useful function and adds convenience to our personal or business lives, to others the IoT represents billions of potential access points to steal data or generally create havoc.
While the IoT provides billions of access points, the regular Internet acts as a catalyst to security breaches. From the very first day that a vulnerability is discovered with a product (known by those ‘in the know’ as ‘zero day’) the means of exploiting the vulnerability is rapidly shared by like-minded individuals anywhere in the world. One of the simplest examples is an IoT device that ships with a factory-configured password that is common to all devices. While ‘savvy’ IT users will change this upon installation, many others will not bother, or be unaware of the need to do so. Unfortunately, this password will rapidly become common knowledge allowing easy access to networks once the device is connected.
There are plenty of ways that cyber-attackers can gain access to a private wireless network and, although a weak or non-existent password is one of the most popular ways, there are plenty of others. One crucial weakness is the fact that networks generally assume that any other device on the same network is ‘friendly’ and can be trusted, which is mostly true but definitely not always the case. Unfortunately, this type of attack is somewhat more challenging to protect against.
In our highly connected world it is very hard for any product or device with weak security to hide for long. These days, breaches are no only inconvenient; they are highly expensive with governments imposing huge fines for careless security. In fact, device manufacturers are rapidly learning that, while it may be expensive to implement good security, the cost of clearing up after a breach when a device is on the market is often far higher than doing the job properly in the first place.
A big part of the challenge is that relatively few people fully understand security needs. Many people believe that what they have done will be adequate, and they continue in this belief – until they get breached.
Trust is earned
These days, software is far more important than hardware in defining the functionality of the devices that we use. Nowhere is this more true than with the devices that form the nodes of the IoT; these are almost exclusively based on a microcontroller that runs on embedded software. Anyone who can gain control of the software can gain control of the microcontroller and whatever the node is controlling – meaning that IoT breaches can have physical consequences, not just the loss of data. To guard against this, it is imperative that the software that is loaded into and executed by the microcontroller has not been changed or tampered with by any unauthorised party. This process of verification is known as ‘establishing a Root of Trust’.
The industry uses the term ‘immutable’ to refer to software that cannot be changed. In general, all software can be changed but, through applying the right technology, any changes can be detected and this is the method by which the Root of Trust is maintained. Every time software is loaded, certification and authentication should be used to verify it. It is also important that the storage media (often NVRAM) has its own security mechanisms that allow the code to be locked down to prevent unauthorised tampering.
A further challenge here is the popularity of updating firmware remotely, known as Firmware-over-the-air (FOTA). This is particularly challenging if the communications link itself is not secure.
Hash Codes
Different levels of security exist for IoT device and the most appropriate is selected based upon the nature of what is being protected. The real issue is detecting that something such as code or data has been tampered with and, if this is detected, then if is often safer to just ignore that data. Different methods exist to achieve this, but hash codes are one of the most popular.
Hash codes can be likened to a digital fingerprint in that they create a unique identifying code by applying a mathematical algorithm to a digital asset. The resulting value is unique to that asset. The verification process is then simple as the hash code is regenerated using the same algorithm and the two hash codes are compared. The use of hash codes is faster and easier than comparing the entire contents of the asset against a known ‘good’ version and offers better security than a simple checksum.
If a digital asset is sent with its hash code then the receiving system can check whether any changes have been made since the hash code was generated, allowing measures such as deletion or quarantining to be applied if the hash codes do not match.
There are several algorithms that are used to generate hash codes although the SHA-256 is probably the most popular in current use. One challenge is that executing hash code algorithms can require a powerful processor and, therefore, consume significant energy. This is not desirable within the IoT and many processors may not have the required performance, so a few MCUs include an in-built hardware accelerator that executes the SHA-256 algorithm to generate hash codes.
Another approach is to use a separate IC to accelerate the cryptographic functions. This allows the use of a less powerful device as the main MCU that requires less power as the basis of a secure system, while continuing to work within a Root of Trust environment that supports secure software execution.
One way this can be achieved is to use Maxim Integrated’s DS28C36 secure authentication IC. This device creates a Root of Trust for secure booting or FOTA upgrades in an embedded system. The DS28C36 can be used with any MCU and external memory.
 Figure 1: The DS28C36 Secure Authenticator IC from Maxim Integrated.
Figure 1: The DS28C36 Secure Authenticator IC from Maxim Integrated.
Using a combination of SHA-256 hash codes and public and private keys, the DS28C36 is able to validate software prior to execution on the MCU. A combination of symmetric and asymmetric features is used alongside private and public keys to achieve this check. Public and private keys are manufacturer-generated in a secure environment – normally their own factory or laboratory. The private key is held securely and never leaves the manufacturer’s control so it cannot be compromised. This private key is used to encode the firmware and the relevant public key is embedded directly into the device.
When a system powers up, the firmware (encrypted with the private key) is loaded from RAM, but it is not executed until it has been checked. The hash code is retrieved by the boot manager within the MCU and sent to the DS28C36. The Maxim device then uses its embedded SHA-256 hardware to generate another hash code for the firmware. Using the embedded hash code that is stored inside the firmware’s certificate (the one generated with the private key by the manufacturer) a comparison can be made. If the comparison shows the hash codes to be identical, then the code can be executed and the DS28C36 sends a hardware signal via GPIO to inform the MCU. This external IC provides a low cost and easy approach to creating a strong Root of Trust, even with the most basic MCU. Maxim offer an evaluation kit (DS28C36EVKIT) for engineers that want to develop a rapid prototype.
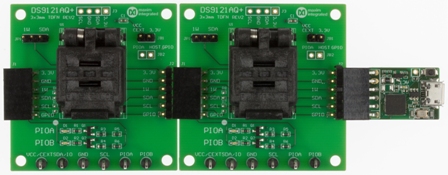 Figure 2: The DS28C36EVKIT Board.
Figure 2: The DS28C36EVKIT Board.
Symmetric or asymmetric encryption – which is best?
Almost since the start of time, ciphers (or codes) have been used to encode information that people wanted to keep secure. The symmetric method is the easiest to comprehend, as it is similar to using a lock. As long as you have a key, the lock can be opened – and any faithful reproduction of the key will open the lock, whoever is using it. In the digital world, the sender uses a key to encode data and the recipient uses the same key to decrypt it. However, much the same as physical keys, anyone who has a copy of the key can open the lock, or in this cast, decrypt the data. If the key is intercepted or given away, then the data is no longer secure.
The symmetric key is so reliant on the security of the key that, if discovered, could be posted online. With the scale of the IoT, this could potentially open up millions of devices right across the world to malicious interference.
As a different approach, the asymmetric key approach uses a pair of keys (private and public), with the private key being held securely so that only the manufacturer of the device knows it. There is no technical difference between the keys as they are generated, one is selected to be the ‘private’ key and it is never knowingly disclosed. The ‘public’ key can be shared – it could even be posted online or written on the device as, without the private key, it is useless to almost everyone. This ability to distribute the public key is a core benefit of using asymmetric keys.
A single algorithm creates both keys – they are different but work together as a pair, meaning that data encrypted with one key can be decrypted with the second key. However, even with knowledge of the public key, the private key cannot be reverse engineered – so the root of the system remains secure.
As the public key is in the public domain, anything encrypted with it cannot be trusted but anything that has been encrypted with the private key (assuming it has not been compromised) can always be trusted and be decrypted using the public key. This clearly demonstrates the value of hash codes in the authentication process.
The ATECC608A crytpo-authentication device from Microchip Technology is just one way of implementing asymmetric keys. Able to store up to 16 different keys, this sophisticated cryptographic co-processor offers hardware support for asymmetric signing, verification and key agreement. This is achieved through the use of Elliptic Curve Digital Signature (ECDSA: FIPS186-3), Elliptic Curve Diffie-Hellman (ECDH: FIPS SP800-56A) and NIST Standard P256 Elliptic Curve Support. Apart from secure boot and protected download features, the ATECC608A supports hardware acceleration for symmetric algorithms such as SHA-256 and HMAC. It also offers encryption and decryption for AES-128.
 Figure 3: The ATECC608A from Microchip Technology.
Figure 3: The ATECC608A from Microchip Technology.
One of the greatest benefits of the ATECC608A is its speed – it is able to run asymmetric cryptographic functions up to 1000 times faster than a software-based solution on a normal MCU. It also supports random private key generation, keeping the key secure on the device – in fact, multiple public / private key combinations can be stored securely. Each time a private key is generated, the corresponding public key is generated – although this can also be done separately if required / preferred.
Security for the Internet
By definition, a significant number of IoT devices require a connection to cloud-based services to function fully. Online criminals tend to focus on devices that connect to financial services and especially want to seek out devices that store private keys locally with insufficient security.
If a private key is obtained or compromised then counterfeit devices can be created and these would become trusted as they would appear secure. This risk demonstrates the importance of strong security being implemented through devices such as Microchip’s ATECC608A.
The same technologies can be used to secure the cloud services that are essential to the functionality of hardware devices such as smartphones or tablets. Manufacturers create private keys en-masse in their secure environment and embed these on a secure cryptographic co-processor (such as the ATECC608A). These keys are then uploaded to the server owned by the cloud service provider, via a TLS-secured connection. This can then be used to validate messages sent via connected devices – Amazon Web Services (AWS) use this exact process for their Bring Your Own Certificate (BYOC) functionality.
Summary
The size and scale of the IoT could hardly have been predicted and the billions of devices and associated services offer multiple potential attack entry points for criminals. As it is so highly integrated, it often goes unseen – but the risk is very real – and drives the need for effective security measures in all connected devices. While this may seem complex, manufacturers such as Microchip Technologies are delivering devices and solutions that make effective security easier than it has ever been.
Authorised Distributor
www.mouser.com