The Internet of Things is a rapidly evolving fire that simply refuses to die down. The amount of data and information that is being processed and shared in this ever growing network of connected entities has become a global powerhouse today. This rapid and seamless exchange of data can be traced back to one thing – connectivity.
Connectivity: Where does it begin?
Some of the main challenges related to building a strong and viable network include a plethora of issues such as security, scalability, reliability, energy efficiency, interfacing and routing of various devices to name a few. Addressing these issues can begin with what is known as communication protocols. These protocols can provide better adapted solutions to a superior IOT network.
One of the most widely used and popular protocols used in low data rate WPAN (personal area networks) is the IEEE 802.15.4. This protocol has by far become the standard for low power and data use and has also formed the basis for other wireless networks like Zigbee and Wireless HART. Standardized back in 2003 by IEEE, this protocol is highly tolerant of noise and interference and also offers link reliability. It also allows for multiplexing of multiple users or nodes to the same channel at the same time. IEEE 802.15.4 also utilizes both star and mesh network topologies which explains its highly reliable behaviour. Its various applications include use in industrial IOT, RFID and powering smart grids.
Zigbee
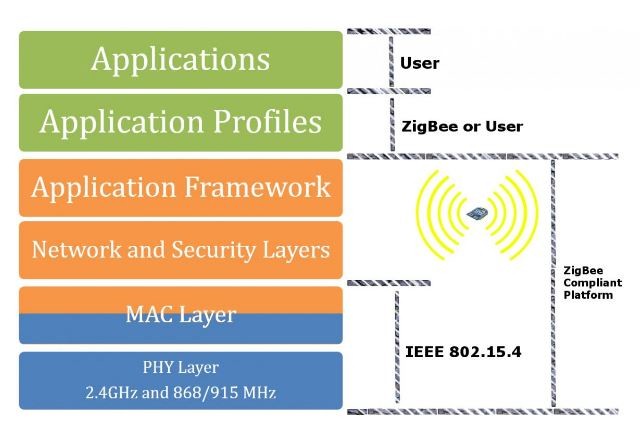 Zigbee has been the defining standard for use in IOT currently. Zigbee can be considered as an extension of the functionalities of IEEE 802.15.4. Zigbees’ capabilities extend beyond just the physical layers but also apply all the way from networking to application layers in IOT networks. Due to these enhancements Zigbee employs authentication of valid nodes, encryption for security, data routing and forwarding capability that enables mesh networking thus providing an overall superior and sophisticated network than most wireless technologies that are being employed today. The mesh topology also increases reliability between connected devices in terms of self- configuration and self- healing networking. Zigbees’ applications include building automation, home automation, smart grids and telecom services.
Zigbee has been the defining standard for use in IOT currently. Zigbee can be considered as an extension of the functionalities of IEEE 802.15.4. Zigbees’ capabilities extend beyond just the physical layers but also apply all the way from networking to application layers in IOT networks. Due to these enhancements Zigbee employs authentication of valid nodes, encryption for security, data routing and forwarding capability that enables mesh networking thus providing an overall superior and sophisticated network than most wireless technologies that are being employed today. The mesh topology also increases reliability between connected devices in terms of self- configuration and self- healing networking. Zigbees’ applications include building automation, home automation, smart grids and telecom services.
RFID
RFID or otherwise known as Radio Frequency Identification has become common place nowadays. RFID works on a principle similar to that of identification of barcodes and QR codes. Data is digitally encoded in RFID tags which can be later read by a card reader. RFID works on a principle derived from Automatic Identification and Data Capture (AIDC) technology but is wireless instead. 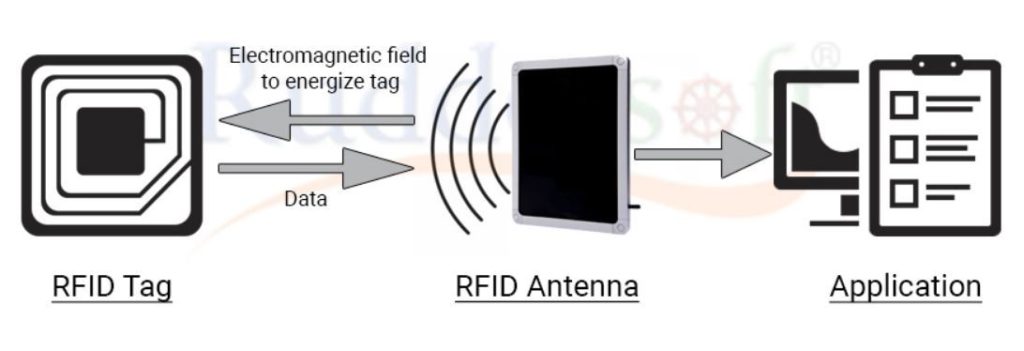 RFID tags cosist of an IC and an antenna which in turn helps in transfer of data to passive card readers through magnetic induction. RFID is very reliable in terms of security and is used for ID badging, personnel tracking, and asset tracking among various other applications.
RFID tags cosist of an IC and an antenna which in turn helps in transfer of data to passive card readers through magnetic induction. RFID is very reliable in terms of security and is used for ID badging, personnel tracking, and asset tracking among various other applications.
NFC
NFC or Near Field Communication technology is a slightly downgraded version of RFID but is preferable for data transfer in close proximity. NFC works similar to RFID with the help of magnetic induction but has a communication range of around only 20cm. NFC has 3 modes of operations namely- peer to peer, read/write and card emulation all of which deal with the exchange of information of through physical contact with smart phones. Smartphone based payments is one of the widely used applications of NFC.
Bluetooth
Bluetooth similar to NFC and RFID is a wireless technology preferable for short range communication. Bluetooth has the added advantage of maintaining high levels of security and has cable replacement protocols in place. It works on Ad-hoc technology which is otherwise known as Ad- hoc piconets. Bluetooth operates on various classes depending upon the range over which data is to be transferred and supports a data rate of 1mbps. It has a sophisticated connection establishment system which includes inquiry, paging and connection.
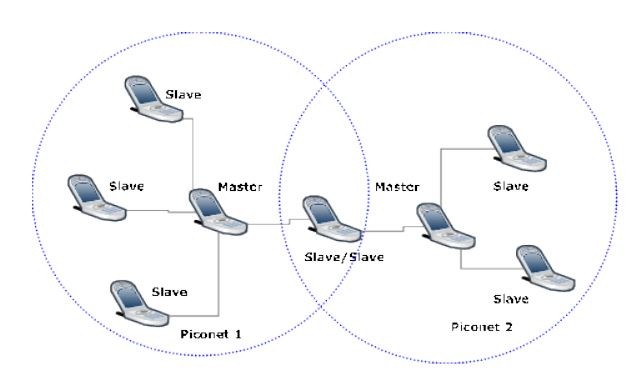 Bluetooth operates through a network topology known as piconets. Each piconet consists of a master and slave devices that help in extending the security, scalability and reliability of the entire network. Piconets are self configuring and self healing which helps in easy pairing and connection of devices. A group of piconets together form what is known as a scatter net. This technology makes Bluetooth a very effective form of data transfer.
Bluetooth operates through a network topology known as piconets. Each piconet consists of a master and slave devices that help in extending the security, scalability and reliability of the entire network. Piconets are self configuring and self healing which helps in easy pairing and connection of devices. A group of piconets together form what is known as a scatter net. This technology makes Bluetooth a very effective form of data transfer.
Z-wave
Z- wave is the users choice for communication among devices used for home automation. It uses radio frequencies for signalling and control and also employs a mesh topology which can support a network of 232 nodes. A central network controller device sets up and manages a Z- wave network. Each logical Z- wave network has one home ID and multiple node IDs for the devices in it. This ensures that nodes with different home IDs cannot communicate with each other. The above features show that Z- wave is ideal for home automation. Z- wave also has an advantage over Zigbee about the fact that it is user friendly and can be incorporated into a network system very easily.
A COMPARITIVE STUDY OF THE VARIOUS PROTOCOLS
| Characteristics | IEEE 802.15.4 | ZIGBEE | RFID | NFC | BLUETOOTH | Z-WAVE |
| Frequency bands | 2.4 GHz | 2.4 GHz | 125 kHz,
13.56 MHz, 902-928 MHz |
125 kHz,
13.56 MHz, 860 MHz |
2.4 GHz | 868 MHz – 908 MHz |
| Topology | Star, Mesh Network | Star, Mesh, Cluster Network | P2P Network | P2P Network | Star- Bus Network | Mesh Network |
| Power | Low power | Low power | Ultra low power | Very low power | Low power | Low power |
| Network | WPAN | WPAN | Proximity | P2P Network | WPAN | WPAN |
| Range | Short range
(10 m to 100 m) |
Short range
(10 m to 100 m) |
Short range
(200 m) |
Short range
(20 cm) |
Short range
(15 m to 30 m) |
30m to 100m |
| Features | Commonly used internal access | Mesh Network | Low Cost | Security | Low power consumption | Simple protocol |
| Common Applications | Monitor and control via internet | Home industry monitoring and controlling | Tracking inventory, personnel access | Payment, Access | Wireless headsets, audio applications | Home monitoring and control |
The above communication protocols are just a few that can help expand the notion of a safe and reliable network employing IOT. The impact and future of connectivity rests on how people and companies will distinguish themselves with solutions to a better IOT.
Author:
Teja Sai Marellapudi
3rd Year Student, B.Tech. (E.C.E)
VNIT, Nagpur, India
Email: tejasaimarellapudi@gmail.com
Phone: +918801065660